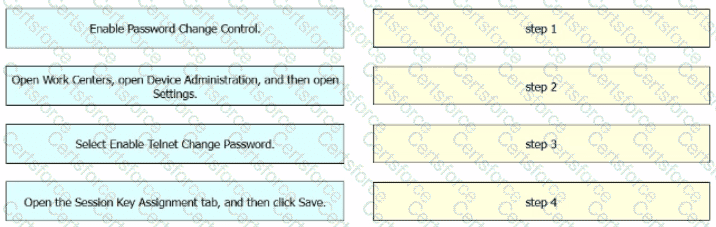
Refer to the exhibit.

An engineer must configure Cisco ISE to be used as the TACACS+ server for any administrator that signs into the router. Users must be able to change their Telnet password through the TACACS+ server. Drag and drop the configuration steps from the left into the sequence on the right.
Submit